Shadow IT: Navigating the Cybersecurity Challenge
Shadow IT, the practice of using technology systems and services without explicit IT department approval, is reshaping the cybersecurity landscape. This trend is fueled by the accessibility of cloud-based applications, which employees can adopt independently, often bypassing traditional security protocols. A Gitnux report reveals that 66% of companies believe Shadow IT diminishes IT department efficiency, while 53% of CIOs find it hampers their ability to enforce security policies. As organizations increasingly rely on digital tools, the unchecked growth of Shadow IT poses significant risks, expanding the attack surface and exposing sensitive data to potential breaches. Understanding and managing this phenomenon is crucial for maintaining robust cybersecurity defenses.
Shadow IT: Expanding Your Attack Surface
Unseen Threats: The Proliferation of Shadow IT
Shadow IT, defined as the use of information technology systems, devices, software, applications, and services without explicit IT department approval, has become a significant concern for organizations worldwide. This phenomenon is primarily driven by the ease of access to cloud-based services and applications, which employees can use without the need for formal approval. According to a Gitnux report, 66% of companies feel that Shadow IT reduces IT department efficiency, and 53% of CIOs report that it impacts their ability to enforce security policies effectively.
The Expanding Attack Surface
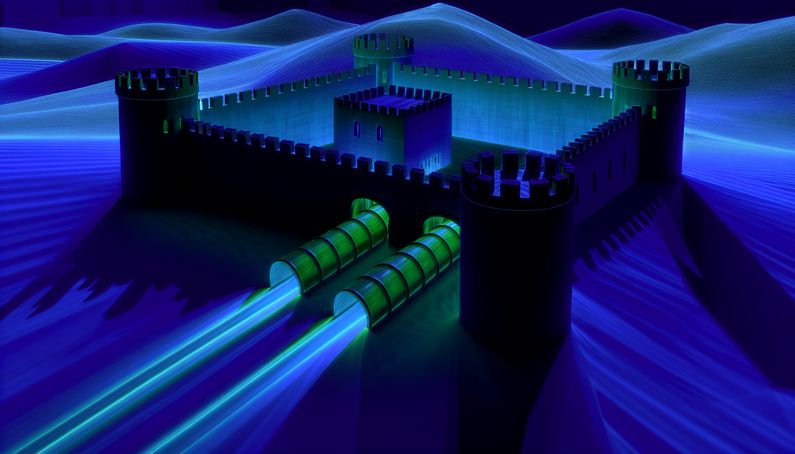
Imagine your organization’s network as a fortress. Shadow IT is like secret tunnels being dug under the walls, expanding the attack surface and making it vulnerable to cyber threats. Unauthorized applications and services can lead to data breaches, as these tools often lack the security measures implemented by approved systems. A Kyndryl and AWS report highlights that 54% of large organizations experienced cyberattacks over the last 12 months, emphasizing the need for preemptive measures against emerging IT risks.
Identifying Shadow IT: Techniques and Challenges
One of the most effective methods to uncover Shadow IT is subdomain enumeration. As highlighted by Bleeping Computer, developers may deploy new systems at will, but to make them accessible, they almost always require a subdomain. This method allows security teams to identify unauthorized systems and applications that are otherwise hidden from view.
However, identifying Shadow IT is not without its challenges. The sheer volume of applications and services available makes it difficult for IT departments to keep track of all the tools employees might be using. Additionally, the use of personal devices for work purposes further complicates the identification process, as these devices may not be subject to the same monitoring and security protocols as company-issued hardware.
The Risks of Shadow IT: Data Breaches and Compliance Issues
The use of Shadow IT can lead to significant security vulnerabilities, including data breaches and compliance issues. Unauthorized or unsecured IT systems can expose sensitive data to hackers, malware, or insider threats. Data breaches can result in financial losses, reputational damage, legal liabilities, and regulatory penalties. As noted by Lansweeper, security vulnerabilities and compliance challenges are among the most significant risks associated with Shadow IT.
Moreover, the use of unauthorized applications can lead to fragmented and inefficient IT operations, as noted by Grip Security. This fragmentation can undermine regulatory compliance efforts, as organizations may not have full visibility into all the tools and services being used within their networks.
Strategies for Mitigating Shadow IT Risks
To effectively manage Shadow IT, organizations must implement a combination of policies, education, and technology. Establishing clear IT policies and educating employees about the risks of Shadow IT are crucial steps in mitigating its impact. According to Lansweeper, leveraging monitoring tools and fostering collaboration between IT and business units can also help manage Shadow IT effectively.
Providing user-friendly, approved alternatives and involving employees in the selection process can encourage the use of sanctioned tools. Regular training and clear communication about the risks of Shadow IT can further help curb its prevalence. Additionally, organizations should consider implementing advanced monitoring and detection tools to identify unauthorized applications and services in real-time.
The Role of Employee Behavior in Shadow IT
Employee behavior plays a significant role in the proliferation of Shadow IT. As noted by Grip Security, unmet employee tech needs and perceived bottlenecks in corporate protocols often drive employees to seek out unauthorized tools and services. Understanding these behaviors and addressing the underlying causes can help organizations reduce the prevalence of Shadow IT.
By involving employees in the decision-making process for selecting approved tools and services, organizations can ensure that their needs are met while maintaining security and compliance. Additionally, fostering a culture of open communication and collaboration between IT and business units can help bridge the gap between employee needs and organizational policies.
The Future of Shadow IT: Trends and Predictions
As organizations continue to adopt cloud-based services and applications, the prevalence of Shadow IT is expected to increase. According to a Teal report, the migration to the cloud and the availability of Software as a Service (SaaS) applications are driving the growth of Shadow IT, as these tools are accessible to employees over the internet, from anywhere, and at any time.
To address this growing challenge, organizations must adopt a proactive approach to managing Shadow IT. This includes implementing advanced monitoring and detection tools, fostering a culture of collaboration and communication, and continuously educating employees about the risks and consequences of using unauthorized tools and services.
By taking these steps, organizations can effectively manage Shadow IT, reduce their attack surface, and protect their sensitive data and systems from cyber threats.
Final Thoughts
The rise of Shadow IT is an inevitable consequence of the digital transformation sweeping across industries. As employees seek more efficient tools to enhance productivity, the challenge for organizations is to balance innovation with security. By implementing comprehensive policies, fostering open communication, and leveraging advanced monitoring technologies, businesses can mitigate the risks associated with Shadow IT. The Kyndryl and AWS report underscores the importance of proactive measures to safeguard against cyber threats. As we look to the future, embracing a collaborative approach between IT departments and employees will be key to managing Shadow IT effectively and securing organizational data.
References
- Gitnux. (2025). Shadow IT statistics. https://gitnux.org/shadow-it-statistics/
- Kyndryl and AWS. (2025). Shadow IT risks. https://www.kyndryl.com/au/en/perspectives/articles/2025/02/shadow-it-risks
- Bleeping Computer. (2025). Shadow IT is expanding your attack surface: Here’s proof. https://www.bleepingcomputer.com/news/security/shadow-it-is-expanding-your-attack-surface-heres-proof/
- Lansweeper. (2025). Effective shadow IT management in 2025: Best practices. https://www.lansweeper.com/blog/itam/effective-shadow-it-management-in-2025-best-practices/
- Grip Security. (2025). Understanding shadow IT: Cyber security strategy. https://www.grip.security/blog/understanding-shadow-it-cyber-security-strategy
- Teal. (2025). The impact of shadow IT on cybersecurity. https://tealtech.com/blog/the-impact-of-shadow-it-on-cybersecurity/



